Powerful enterprise protection starts here.
Secure your business with multi-layer protection, device trust security, AI-powered defenses, and robust privacy — keeping your teams safe, wherever they work.
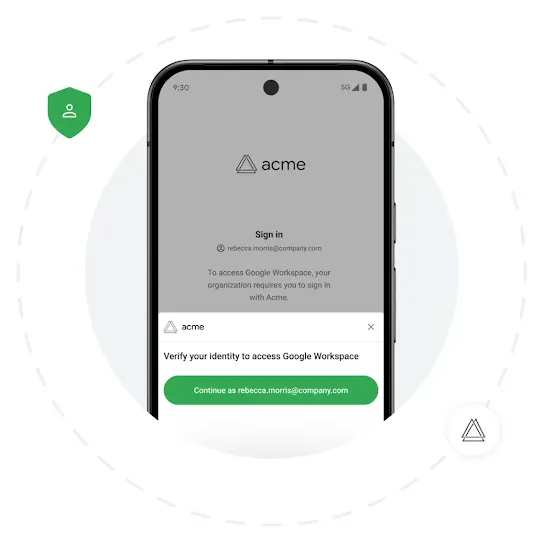
Enable secure access on mobile
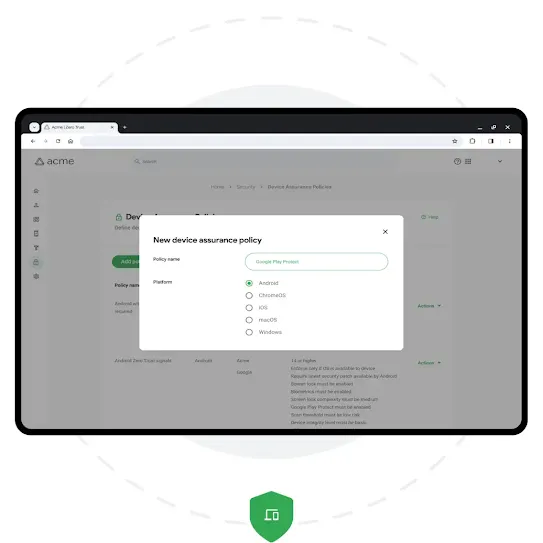
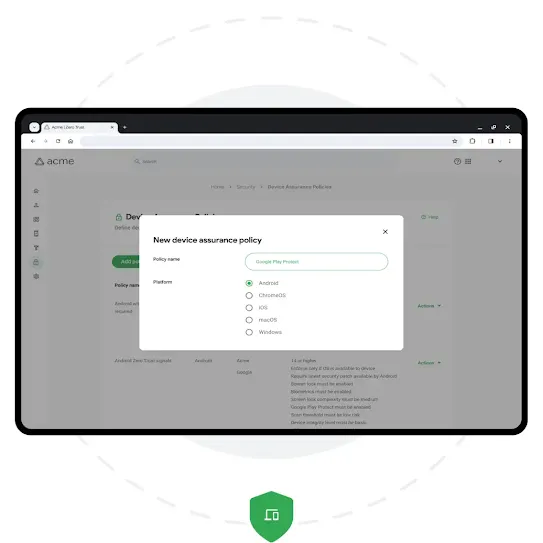
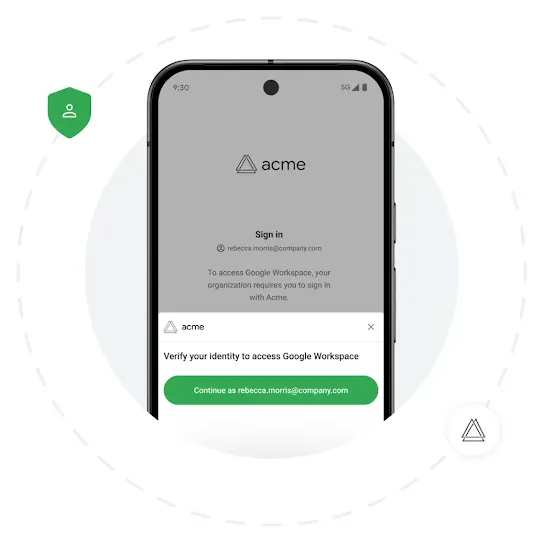
Introducing Device Trust from Android Enterprise
Device Trust from Android Enterprise helps protect devices, data, and privacy, empowering employees to work from anywhere.²
Learn more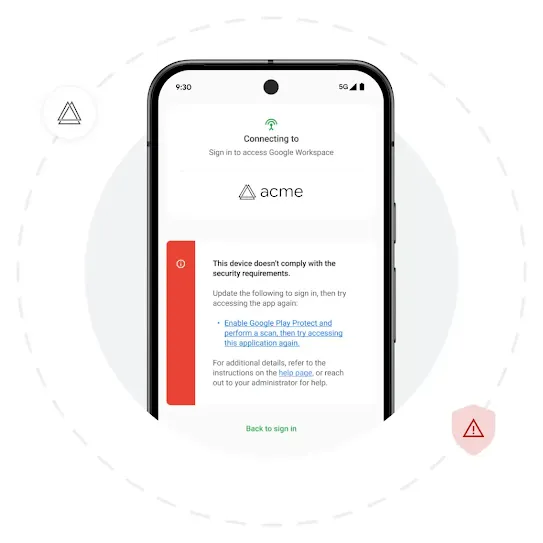
Security for the modern workplace
Flexible solutions for diverse use cases
The employee experience, uninterrupted.
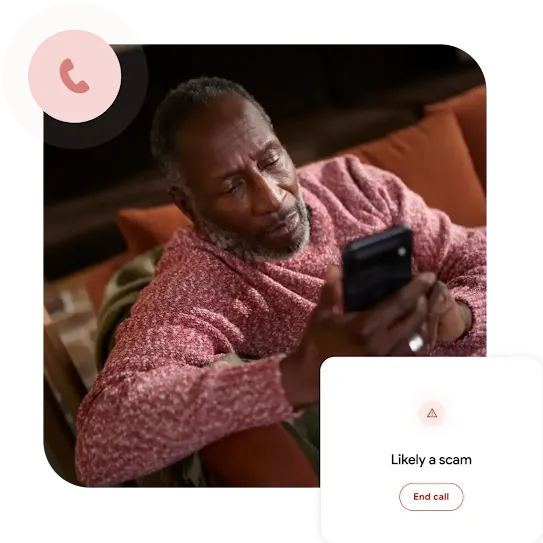
Help stop scams before they start.
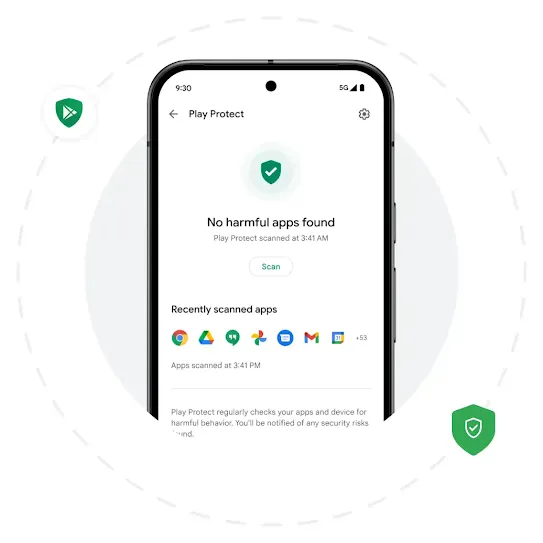
Defend against malware with machine learning.
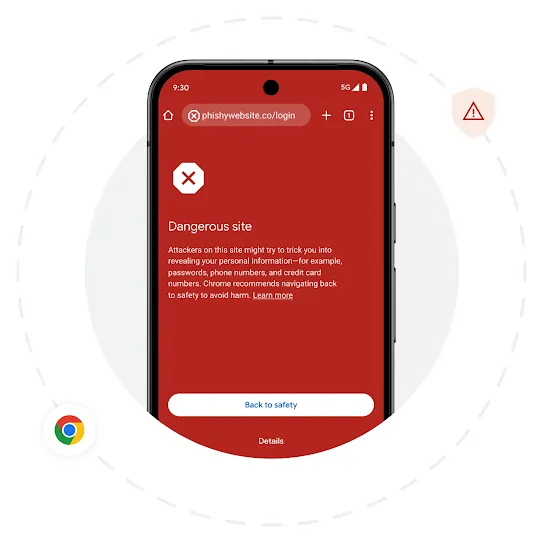
Protect employees online with Google Safe Browsing.
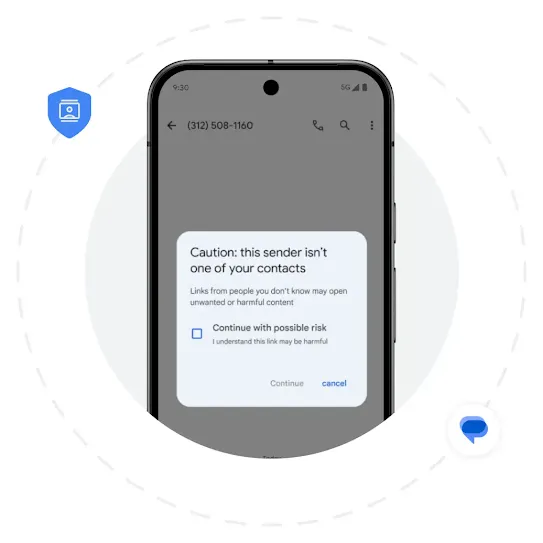
Block harmful links in Google Messages.
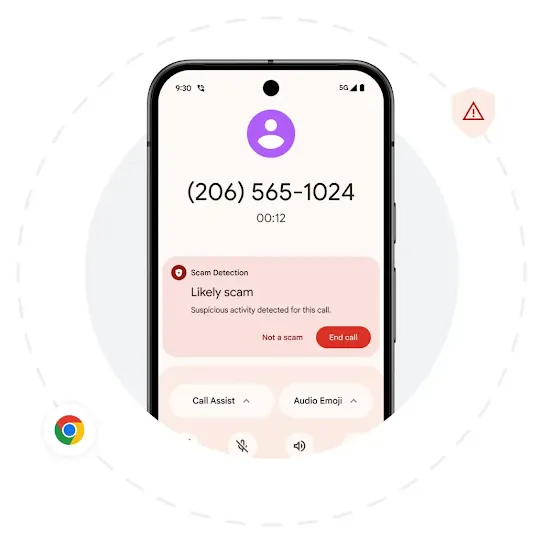
Get alerted to phishing messages and calls.
Deploy multi-layered protection.
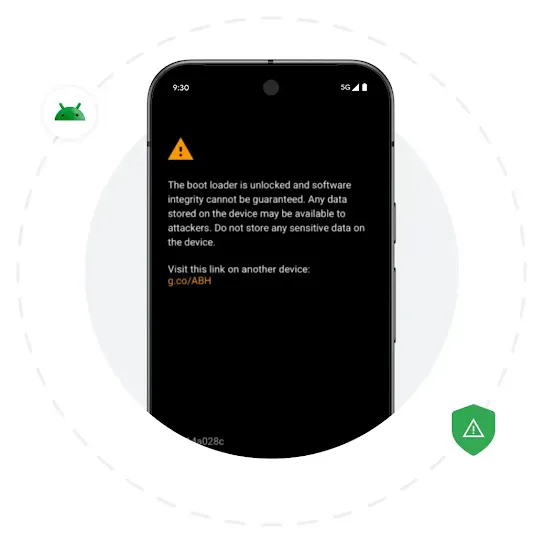
Rely on built-in hardware security.
Protect your business with a hardened OS
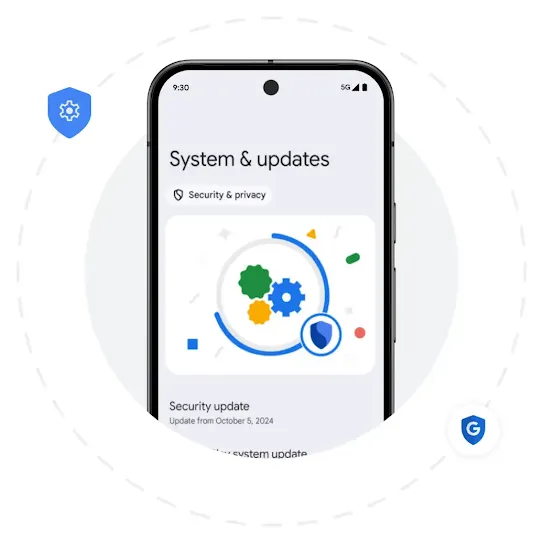
Receive timely security patches and OS updates.
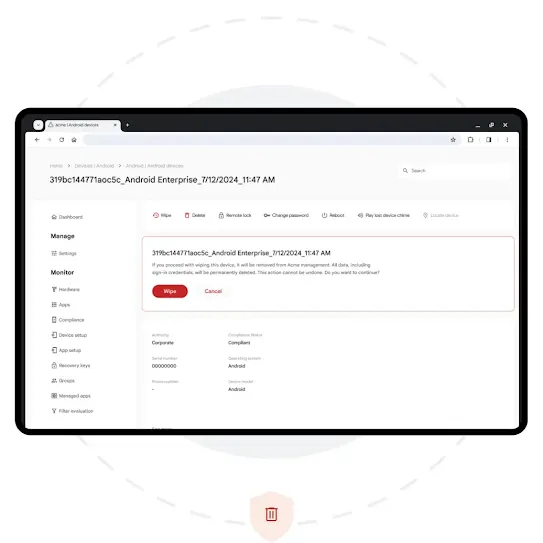
Lock down your business data.
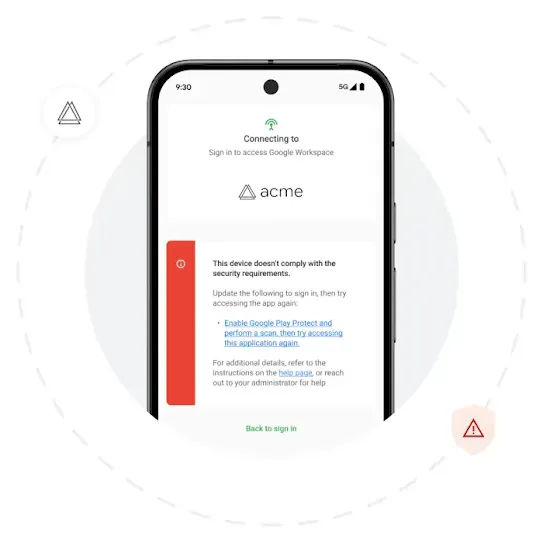
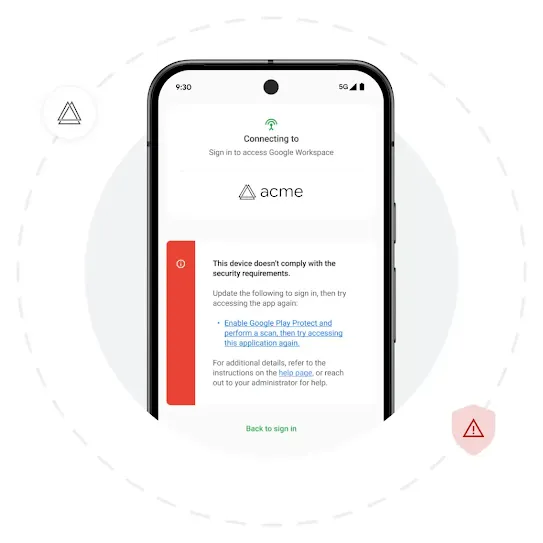
Take a Zero Trust approach to mobile.
Security for the modern workplace
Flexible solutions for diverse use cases
The employee experience, uninterrupted.
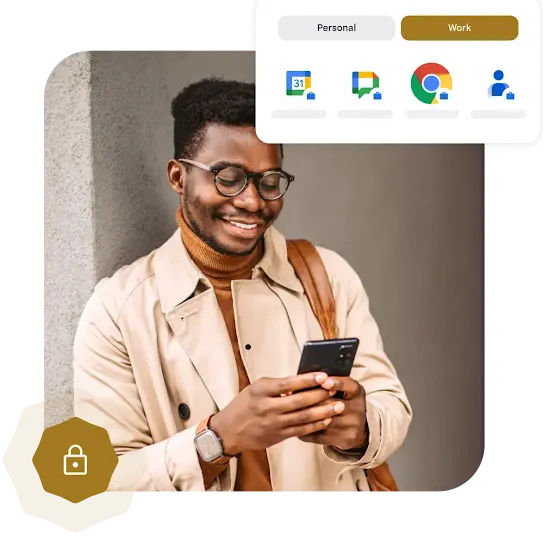
Prevent data breaches.
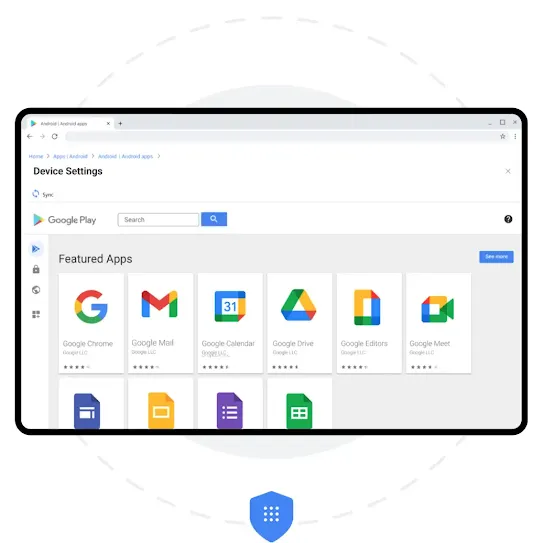
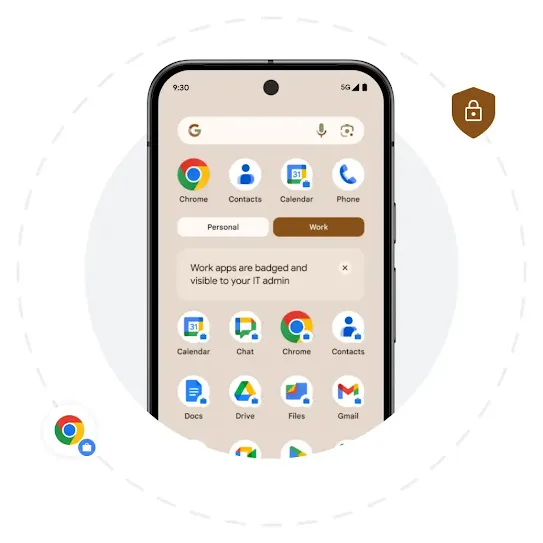
Choose what apps employees can access.
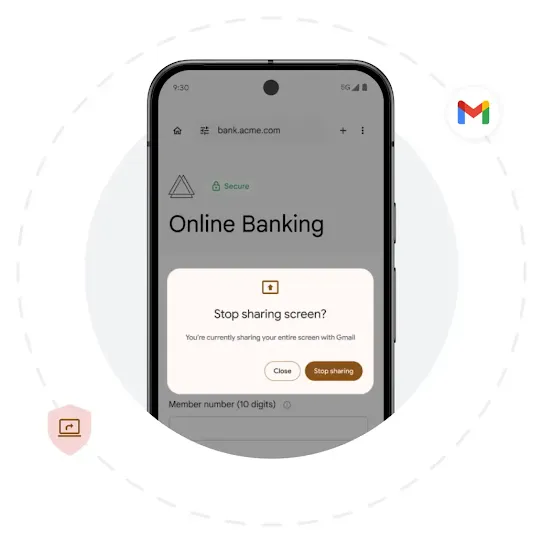
Define privacy on your terms.
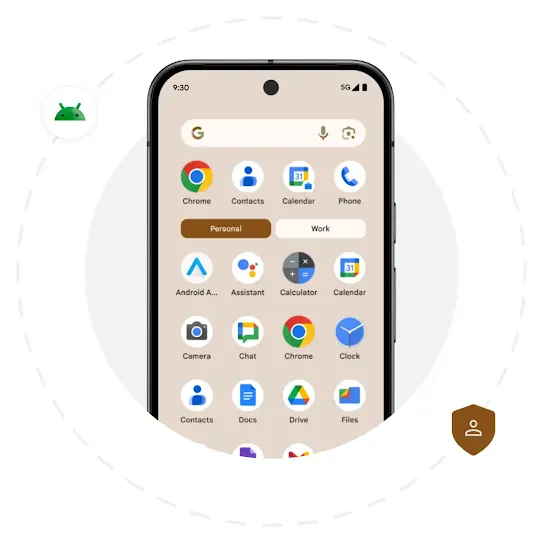
Protect employee privacy with a personal profile.
Ensure data privacy for AI tools

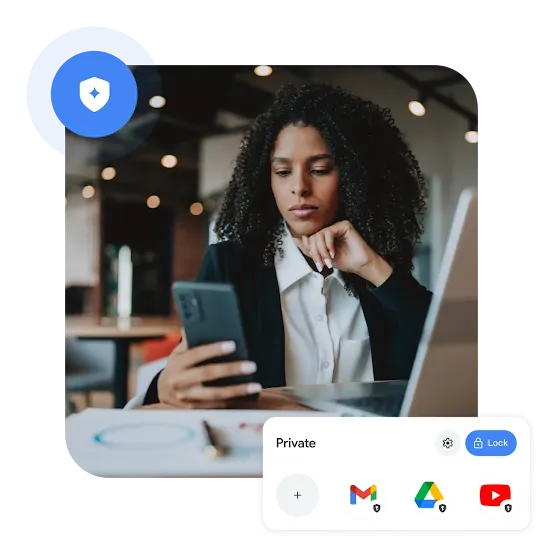
Offer employees a private space.
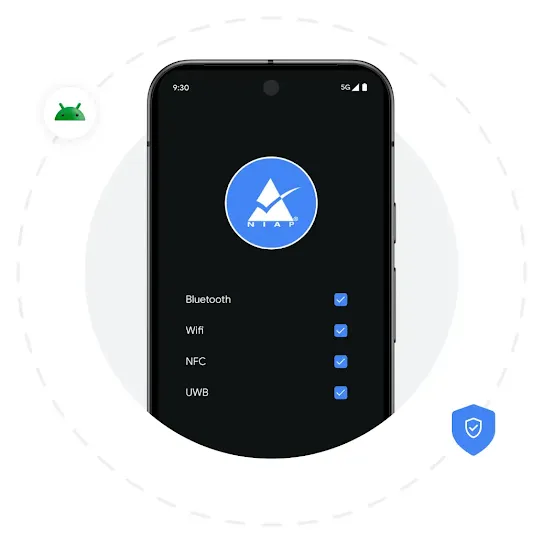
Stay compliant with NIAP requirements.
Fight back against theft.
Track down lost or stolen devices.
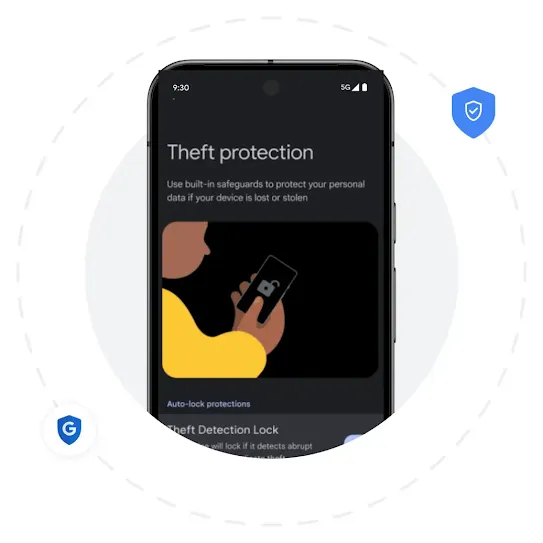
Secure stolen devices with theft protection.